Oops, I made a mistake
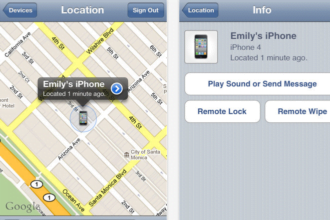
The recent settlement between Accretive Health and the State of Minnesota is one more domino in the growing parade of breach casualties. What makes this case odd is the simultaneous insistence of no wrongdoing or liability, the resignation of their controller and the fact that ePHI (electronic protected health information) was left on a portable device in an employee’s car with no encryption.
No admission of liability
Oops, I made a mistake
The recent settlement between Accretive Health and the State of Minnesota is one more domino in the growing parade of breach casualties. What makes this case odd is the simultaneous insistence of no wrongdoing or liability, the resignation of their controller and the fact that ePHI (electronic protected health information) was left on a portable device in an employee’s car with no encryption.
No admission of liability
The phrase that keeps dancing through my mind is from the latest kids’ mobile app I made the mistake of downloading onto my phone. My daughter’s favorite snippet is a cheery little song that highlights “Oops, I made a mistake” roughly 50 times within a single 3 minute clip.
The Organizational Requirements of the HIPAA Security Rule defined in 164.504(e) requires contracts between Covered Entities (CEs) and Business Associates (BAs) to extend the chain-of-trust for the explicit purpose of protecting health information. So how can there be no liability if a laptop with unprotected ePHI was left in a vehicle and stolen? One or more of the following must have happened:
- The BA did not have a policy or procedure in place that would have prevented unencrypted ePHI from being stored on a portable device.
- The BA did not have policies or procedures to control the security of the portable device.
- The employee did not follow the policies or procedures of the BA.
- The CEs did not review the policies and procedures of the BA with regards to handling ePHI.
- The BA did not audit its own policies or procedures, or invest in a third party, as part of a HIPAA risk assessment and management plan.
- The CEs did not audit the BA’s policies or procedures to ensure they were protecting PHI appropriately.
In all of the cases above, there is liability on the part of the CE, the BA, and the patient. How can a major healthcare vendor state that it has no liability to protect PHI? Without accepting responsibility or owning liability, how do you improve protections? And who pays a $2.5 MILLION settlement for not doing anything wrong? It’s a terrible example for both CEs and BAs to set to allow this “no liability” myth to pervade the industry.
Maybe Spiderman said it best: “With great power comes great responsibility.”
Hey, if a comic book character can figure it out, I think we should be able to say “Oops, I made a mistake” and then entertain changing our perspective.
CEs, please do:
- Ask for and read what a BA has done to assess and manage HIPAA compliance under the full HIPAA security rule – let’s hope this includes an independent audit, because, let’s face it, you can’t audit yourself legitimately.
- Spend the money to go visit BA facilities – if you think you don’t have the time and money to do that, just think about the cost of a breach.
- Have a proactive and ongoing dialog with BAs about HIPAA compliance and your expectations for handling PHI.
BAs, please do:
- Accept and embrace full responsibility to protect PHI.
- Invest in annual, independent third party audits by a respected HIPAA security authority.
- Embrace and address any areas that would improve the confidentiality, privacy, and availability of PHI.
If you have any questions about your responsibilities under the HIPAA Security Rule, please contact a qualified HIPAA legal counsel or a HIPAA security specialist.
References from the HIPAA security rule:
The Privacy Rule allows covered providers and health plans to disclose protected health information to these “business associates” if the providers or plans obtain satisfactory assurances that the business associate will use the information only for the purposes for which it was engaged by the covered entity, will safeguard the information from misuse, and will help the covered entity comply with some of the covered entity’s duties under the Privacy Rule.
General Provision. The Privacy Rule requires that a covered entity obtain satisfactory assurances from its business associate that the business associate will appropriately safeguard the protected health information it receives or creates on behalf of the covered entity. The satisfactory assurances must be in writing, whether in the form of a contract or other agreement between the covered entity and the business associate.
(e)(1) Standard: Business associate contracts. (i) The contract or other arrangement between the covered entity and the business associate required by §164.502(e)(2) must meet the requirements of paragraph (e)(2) or (e)(3) of this section, as applicable.
(ii) A covered entity is not in compliance with the standards in §164.502(e) and paragraph (e) o this section, if the covered entity knew of a pattern of activity or practice of the business associate that constituted a material breach or violation of the business associate’s obligation under the contract or other arrangement, unless the covered entity took reasonable steps to
cure the breach or end the violation, as applicable, and, if such steps were unsuccessful:
(A) Terminated the contract or arrangement, if feasible; or
(B) If termination is not feasible, reported the problem to the Secretary.
(2) Implementation specifications: Business associate contracts. A contract between the covered entity and a business associate must:
(i) Establish the permitted and required uses and disclosures of such information by the business associate.
The contract may not authorize the business associate to use or further disclose the information in a manner that would violate the requirements of this subpart, if done by the covered entity,
except that:
(A) The contract may permit the business associate to use and disclose protected health information for the proper management and administration of the business associate, as provided in paragraph (e)(4) of this section; and
(B) The contract may permit the business associate to provide data aggregation services relating to the health care operations of the covered entity.
(ii) Provide that the business associate will:
(A) Not use or further disclose the information other than as permitted or required by the contract or as required by law;
(B) Use appropriate safeguards to prevent use or disclosure of the information other than as provided for by its contract;
(C) Report to the covered entity any use or disclosure of the information not provided for by its contract of which it becomes aware;
(D) Ensure that any agents, including a subcontractor, to whom it provides protected health information received from, or created or received by the business associate on behalf of, the
covered entity agrees to the same restrictions and conditions that apply to the business associate with respect to such information.

April Sage, CPHIMS, Director Healthcare Vertical, Online Tech
April Sage has been involved in the IT industry for over two decades, initially founding a technology vocational program. In 2000, April founded a bioinformatics company that supported biotech, pharma, and bioinformatic companies in the development of research portals, drug discovery search engines, and other software systems.
Since then, April has been involved in the development and implementation of online business plans and integrated marketing strategies across insurance, legal, entertainment, and retail industries until her current position as Director Healthcare Vertical of Online Tech.
Contact: asage@onlinetech.com
Recommended Reading:
Five Questions to Ask Your HIPAA Hosting Provider
Online Tech’s BAA Breach Notification Clause
In the Wake of a Healthcare Data Breach
Healthcare Organizations: Seeking a Cloud Provider? BAAs Required
References:
Business Associates from HHS.gov
Uses and Disclosures: Organizational Requirements from HHS.gov (PDF)