Of the 345 incidents reported by HHS and listed on their site under Breaches Affecting 500 or More
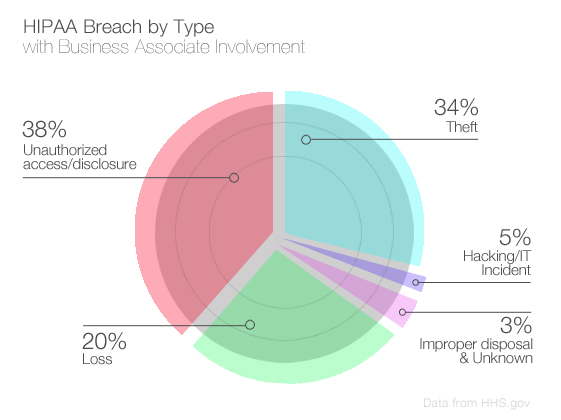
Of the 345 incidents reported by HHS and listed on their site under Breaches Affecting 500 or More Individuals, 74 involved a business associate (21 percent).
An increasing number of recent HIPAA violations are caused or involve a business associate – the Stanford Hospital breach was due to improper disclosure of PHI, and the TRICARE/SAIC incident was due to the theft of unencrypted backup tapes out of the trunk of an employee’s car.

Business Associates and HIPAA Violations
While most of the incidents were isolated – meaning different business associates are involved with each individual company, a few repeats were evident. Med Assets made up for 9.5 percent of the breaches reported with a business associate involved, meaning they affected 6 different companies listed.
Two separate incidents affected multiple covered entities – one set affected 4 different healthcare organizations and the other affected 3 different covered entities.
This data makes apparent the level of preparedness that business associates have when it comes to HIPAA security policies, procedures and training. When employees are improperly trained, they leave the business vulnerable to data theft, loss, hacking and/or simple security negligence within the IT environment, putting covered entities at great risk for a HIPAA violation and accompanying fines.
And when one IT vendor is responsible for PHI from many different hospitals, just one incident can have a significant damaging effect on an exponential amount of patients.
If you are outsourcing your data hosting, put research into finding a HIPAA hosting provider who is audited by a CHP (Certified HIPAA Practitioner) and CHSS (Certified HIPAA Security Specialist). Note, this doesn’t make your company HIPAA compliant, or any less responsible for implementing your own policies and procedures, but it does mean you have taken an active role in researching your vendors to prevent a data breach.
If you need more guidance on HIPAA policies, procedures and training materials, visit ourHIPAA resources section today.