2012 Healthcare Data Breach Update
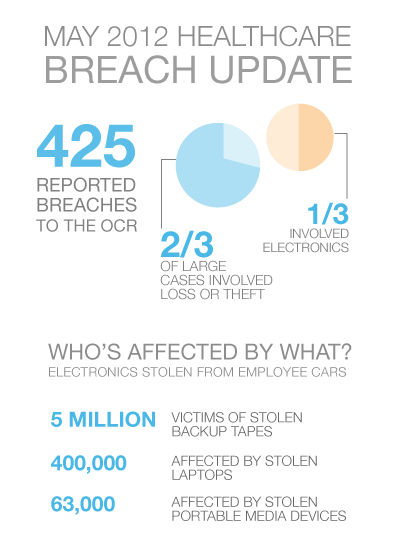
Of the 425 reported breach events to the OCR (Office of Civil Rights), two-thirds of all large breach cases involved loss or theft of information and more than half of these large breaches involved electronic devices.

2012 Healthcare Data Breach Update
Of the 425 reported breach events to the OCR (Office of Civil Rights), two-thirds of all large breach cases involved loss or theft of information and more than half of these large breaches involved electronic devices.
While a BAA (business associate agreement) can help a healthcare organization maintain control and insight into privacy and security practices involved with handling their ePHI (electronic protected health information), risks of storing and transporting ePHI are also of concern, as exemplified by the reported 5 million individuals affected by a breach caused by backup tapes being stolen from an employee’s car.
About 1 million have been victims of lost backup tapes in office renovation situations, and 400,000 affected by theft of a laptop from an employee’s car. Desktop computer theft from offices has affected 943,000 more, and 63,000 have been affected by theft of a portable media device from an employee’s car.
What’s the solution to this seemingly prevalent problem with ePHI? Revert to paper records in a healthcare vault with multiple doors and lock combinations? Restrict ePHI to existing only on non-mobile electronics? Demand counter-reform in the face of federal reform with the advent of EHR system implementation?
The answer is fairly simple but often ignored ‘best practice’ advice.
Aside from the common sense lesson of ‘don’t leave your electronics in your car,’ David S. Holtzman from the OCR recommends storing data on a secure network, not a mobile device. Instead of losing data when you lose your phone or laptop, the data should be stored in a HIPAA compliant data center with standardized network security in place.
Sensitive infrastructure, such as servers, power and network should be protected by restricted access. Using an Intrusion Detection Service (IDS) and monitoring can help notify administrators of a potential breach, and give you the tools to resolve an issue, including times and user activity on a server and network.
As a second choice and additional layer of protection, Holtzman recommends encryption to protect the data, with the cost ranking up as minimal compared to breach fines. For a detailed data on the minimum and maximum fines for breaches by type, visit What is a HIPAA Violation?